Cybersecurity for Finances 2026: Protect $1M Digital Threats

Anúncios
Protecting up to $1 million from digital threats in 2026 necessitates a multi-layered cybersecurity approach, combining advanced technological defenses with informed user practices to secure financial assets against evolving cybercrime.
Anúncios
As we navigate further into the digital age, the landscape of financial security is constantly evolving. By 2026, safeguarding your assets against increasingly sophisticated cyber threats is not just advisable, but absolutely critical. This article delves into the proactive measures and advanced strategies necessary for robust cybersecurity financial protection 2026, ensuring your financial well-being remains uncompromised, even when managing significant sums like $1 million.
The Evolving Threat Landscape in 2026
The digital world of 2026 presents a complex and ever-changing array of threats to personal and corporate finances. Cybercriminals are no longer relying on simple phishing scams; they are employing artificial intelligence, machine learning, and advanced social engineering tactics to breach even the most secure systems. Understanding these evolving threats is the first step in building an impenetrable defense for your financial assets.
Anúncios
The sophistication of cyberattacks has grown exponentially, making it harder for individuals and traditional security measures to keep up. From highly personalized spear-phishing campaigns to ransomware variants that leverage zero-day vulnerabilities, the risks are pervasive and demand a proactive, adaptive approach to cybersecurity.
AI-Powered Cyberattacks and Deepfakes
One of the most alarming developments is the use of AI to automate and enhance cyberattacks. AI can analyze vast amounts of data to identify vulnerabilities, craft highly convincing phishing emails, and even generate deepfake audio or video to impersonate trusted individuals. This makes verification much more challenging.
- Automated Phishing: AI-driven bots can create hyper-realistic emails and messages, tailored to individual targets.
- Deepfake Impersonation: Voice and video deepfakes are used to bypass biometric authentication and trick employees or family members into authorizing fraudulent transactions.
- Adaptive Malware: Malware can now learn and adapt to security measures, making it harder to detect and eradicate.
The financial sector is a prime target due to the high value of potential gains. As such, staying informed about these advanced methods is paramount for anyone looking to protect their assets from digital threats in the coming years.
Fortifying Your Digital Defenses: Core Principles
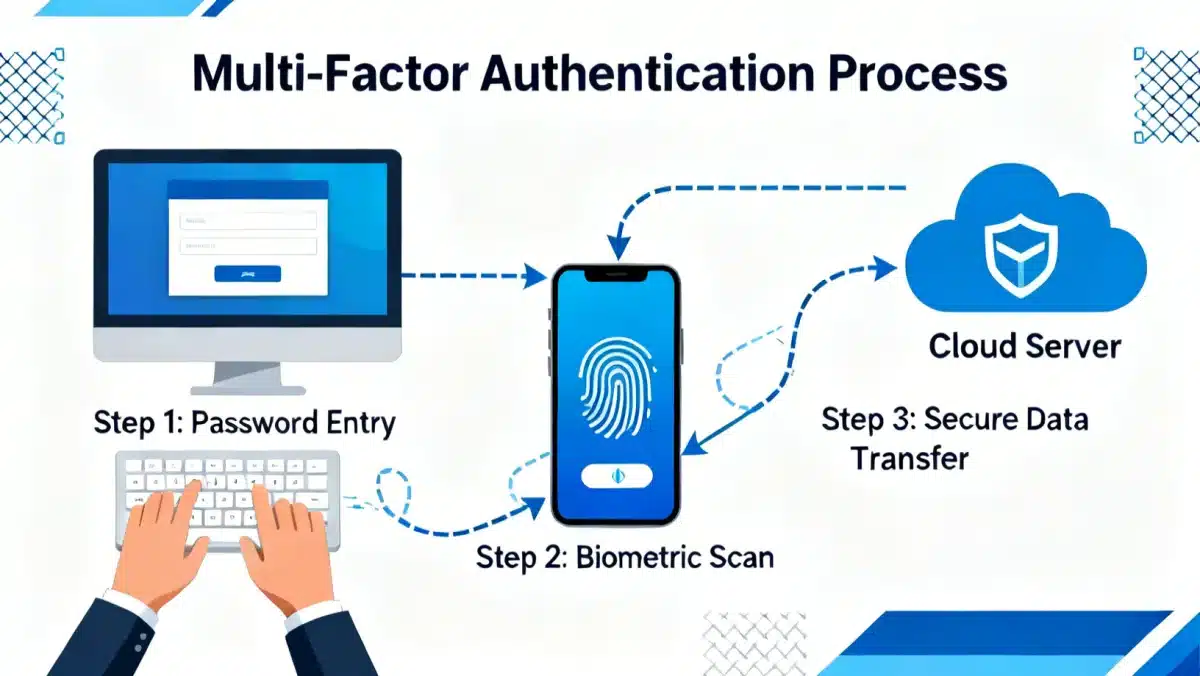
Effective cybersecurity in 2026, standard MFA methods like SMS codes are becoming less secure due to SIM-swapping attacks. Advanced MFA, utilizing biometric data or hardware security keys, offers significantly stronger protection.
- Biometric Authentication: Fingerprint, facial recognition, and iris scans provide highly secure authentication methods.
- Hardware Security Keys: Physical devices like FIDO2 keys offer an unphishable layer of security, making it nearly impossible for remote attackers to gain access.
- Authenticator Apps: Time-based One-Time Password (TOTP) apps generate codes that refresh frequently, adding a strong layer of defense.
Ensuring MFA is active on every financial platform, email account, and cloud service is a critical step in safeguarding your digital identity and, by extension, your financial assets.
Advanced Threat Intelligence and Monitoring
In the dynamic world of 2026, simply reacting to threats is insufficient. Proactive threat intelligence and continuous monitoring are essential for identifying vulnerabilities and potential attacks before they can cause significant damage. This involves leveraging specialized services and tools that provide real-time insights into emerging cyber risks.
For individuals managing substantial assets, this level of vigilance might seem excessive, but the cost of a breach can far outweigh the investment in advanced monitoring. Understanding the tactics, techniques, and procedures (TTPs) of cybercriminals allows for the implementation of preventative measures, rather than merely responding to incidents.
Leveraging AI and Machine Learning for Anomaly Detection
AI and machine learning (ML) are not just tools for attackers; they are powerful allies for defense. These technologies can analyze vast amounts of network traffic and user behavior data to detect anomalies that might indicate a cyberattack in progress. This includes unusual login attempts, large fund transfers, or access from unrecognized locations.
- Behavioral Analytics: AI systems learn your normal financial behavior and flag any deviations, such as an uncharacteristic large transfer or a login from an unusual device.
- Real-time Threat Feeds: Subscribing to services that provide up-to-the-minute information on new malware, phishing campaigns, and vulnerabilities.
- Automated Incident Response: AI can trigger automated responses, such as locking an account or isolating a compromised device, to minimize damage during an attack.
Implementing such advanced monitoring tools provides an early warning system, giving you the time to react and protect your assets effectively.
Securing Your Digital Footprint and Devices
Every online interaction and every device connected to the internet contributes to your digital footprint, which can be a point of vulnerability if not properly managed. By 2026, personal devices are increasingly integrated into financial management, making their security paramount. Protecting your digital footprint involves a holistic approach to device security, network hygiene, and data privacy.
A single compromised device can serve as a gateway for attackers to access your most sensitive financial information. Therefore, maintaining rigorous security standards across all your digital touchpoints is non-negotiable for protecting your assets from evolving digital threats.
Best Practices for Device and Network Security
Regularly updating software, using strong, unique passwords, and encrypting sensitive data are foundational practices. However, in 2026, these measures need to be augmented with more advanced strategies to counter sophisticated attacks.
- Endpoint Detection and Response (EDR): Utilize advanced EDR solutions on all devices to monitor for malicious activity and provide rapid response capabilities.
- Secure Wi-Fi Networks: Always use strong encryption (WPA3) on your home network and avoid public Wi-Fi for financial transactions without a trusted VPN.
- Regular Data Backups: Implement automated, encrypted backups of all critical financial data to secure cloud storage or external drives, protecting against ransomware and data loss.
Adopting these practices significantly reduces the attack surface available to cybercriminals, thereby strengthening your overall financial cybersecurity posture.
The Human Element: Education and Awareness
Even the most advanced technological defenses can be undermined by human error. In 2026, cybercriminals are increasingly targeting individuals through social engineering, exploiting trust and psychological vulnerabilities rather than technical flaws. Therefore, ongoing education and heightened awareness among individuals are critical components of a robust cybersecurity strategy.
Understanding the common tactics employed by attackers empowers individuals to identify and resist these attempts. This includes recognizing phishing attempts, understanding the risks of unsolicited communications, and being wary of urgent or emotionally charged requests that often precede a scam. For those protecting significant assets, this personal vigilance is as important as any software or hardware solution.
Recognizing and Resisting Social Engineering
Social engineering attacks are designed to manipulate individuals into divulging confidential information or performing actions that compromise security. These attacks can take many forms, from seemingly legitimate emails to convincing phone calls from fake support personnel.
- Phishing and Spear-Phishing: Be suspicious of emails or messages asking for personal information, especially if they contain urgent requests or unexpected attachments.
- Vishing (Voice Phishing): Verify the identity of callers who claim to be from banks or financial institutions, especially if they ask for account details or passwords.
- Pretexting: Be cautious of individuals who create a fabricated scenario to gain your trust and access sensitive information. Always independently verify any claims.
Regular training and awareness campaigns can significantly reduce the risk of falling victim to these cunning psychological manipulation tactics, thereby reinforcing your financial cybersecurity.
Financial Institution Collaboration and Legal Recourse
While individual efforts are crucial, the responsibility for financial cybersecurity is also shared with financial institutions. By 2026, banks and investment firms are expected to employ state-of-the-art security measures and provide clear channels for reporting suspicious activity. Understanding your rights and available legal recourse in the event of a breach is also a vital aspect of protecting your assets.
Choosing financial partners with a proven track record in cybersecurity and robust protective policies is a strategic decision. Furthermore, knowing how to react immediately after a potential breach can significantly impact the recovery of lost funds and mitigate further damage. This collaborative approach between individuals and institutions forms a comprehensive shield against digital threats.
Understanding Your Bank’s Security Protocols and Protections
It is imperative to familiarize yourself with the security features and guarantees offered by your financial institutions. Most banks offer fraud protection, but the extent and conditions can vary. In 2026, look for institutions that prioritize advanced encryption, real-time transaction monitoring, and multi-layered authentication for their services.
- Fraud Protection Policies: Understand the limits and conditions of your bank’s fraud liability policies.
- Secure Communication Channels: Use only official and encrypted channels provided by your bank for sensitive communications.
- Cybersecurity Support: Ensure your financial institution offers dedicated cybersecurity support and clear procedures for reporting suspected fraud or unauthorized access.
In the unfortunate event of a breach, prompt reporting to your bank and relevant authorities, such as the FBI’s Internet Crime Complaint Center (IC3), is crucial for initiating recovery procedures and pursuing legal recourse.
| Key Point | Brief Description |
|---|---|
| Evolving Threats | Cybercriminals use AI, deepfakes, and advanced social engineering, requiring adaptive defenses. |
| Advanced MFA | Universal adoption of biometrics and hardware keys for superior account protection. |
| Proactive Monitoring | AI/ML-driven anomaly detection and real-time threat intelligence for early warnings. |
| Human Element | Continuous education and awareness against social engineering are crucial. |
Frequently Asked Questions About Financial Cybersecurity in 2026
In 2026, the biggest threats include AI-powered phishing and deepfake scams, which can impersonate individuals or institutions with significant realism. Additionally, adaptive malware and ransomware exploiting zero-day vulnerabilities pose substantial risks, requiring advanced detection and prevention methods.
Protecting against AI-driven attacks involves using advanced MFA like biometrics or hardware keys, implementing AI/ML-powered anomaly detection on your accounts, and maintaining a high level of skepticism towards any unsolicited communications, even if they appear highly legitimate.
While MFA remains crucial, traditional SMS-based MFA is becoming less secure. In 2026, it’s essential to upgrade to stronger MFA methods such as FIDO2 hardware keys, biometric authentication, or dedicated authenticator apps, which offer better resistance against sophisticated attacks like SIM-swapping.
Financial institutions are expected to provide robust security infrastructure, including advanced encryption, real-time fraud detection, and clear reporting mechanisms. You should choose institutions with strong cybersecurity policies and understand their fraud protection guarantees to ensure your assets are well-covered.
Immediately contact your financial institution to report the suspected breach and freeze your accounts. Change all affected passwords, enable stronger MFA, and report the incident to relevant authorities like the FBI’s Internet Crime Complaint Center (IC3) to initiate recovery and investigation.
Conclusion
The journey to securing your finances in 2026 against digital threats is multifaceted, demanding a blend of advanced technology, unwavering vigilance, and informed decision-making. Protecting up to $1 million requires not only the implementation of robust cybersecurity measures like advanced MFA and AI-driven monitoring but also a deep understanding of the evolving threat landscape. By continuously educating ourselves, fortifying our digital defenses, and collaborating with secure financial institutions, we can navigate the complexities of the digital age with confidence, safeguarding our financial future against even the most sophisticated cyber adversaries.